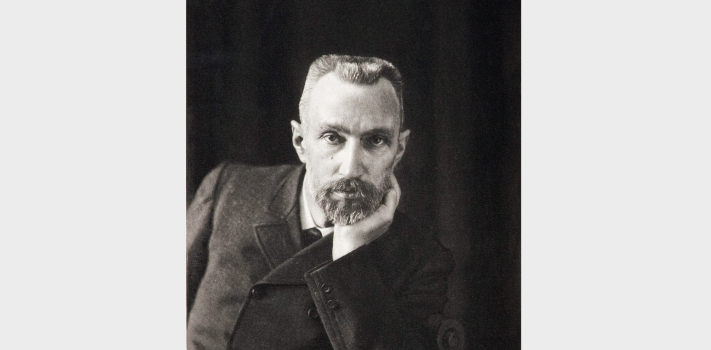
On April 20, 1902, Pierre and Marie Curie isolated the radioactive compound radium chloride.
On April 20th, 2010, an explosion on the Deepwater Horizon oil platform, leased by BP, killed 11 workers and began spewing an estimated 200 million gallons of crude into the Gulf of Mexico for nearly three months, creating the worst known offshore oil spill.
April 20th is also the day that we remember the victims of the Columbine High School tragedy, where two students stormed into a suburban high school in Littleton, Colorado in 1999, at lunchtime with guns and explosives, killing 13 and wounding dozens more in what was, at the time, the nation’s deadliest school shooting. Today, 25 years later, the teachers and other staff members of most schools are still unarmed. And the mass murderers know it, so the massacres continue.
—
SurvivalBlog Writing Contest
Today we present another entry for Round 112 of the SurvivalBlog non-fiction writing contest. The prizes for this round include:
First Prize:
- The photovoltaic power specialists at Quantum Harvest LLC are providing a store-wide 10% off coupon. Depending on the model chosen, this could be worth more than $2,000.
- A Gunsite Academy Three Day Course Certificate. This can be used for any of their one, two, or three-day course (a $1,095 value),
- A Peak Refuel “Wasatch Pack” variety of 60 servings of premium freeze-dried breakfasts and dinners in individual meal pouches — a whopping 21,970 calories, all made and packaged in the USA — courtesy of Ready Made Resources (a $359 value),
- American Gunsmithing Institute (AGI) is providing a $300 certificate good towards any of their DVD training courses.
- Two sets of The Civil Defense Manual, (in two volumes) — a $193 value — kindly donated by the author, Jack Lawson.
Second Prize:
- A SIRT STIC AR-15/M4 Laser Training Package, courtesy of Next Level Training, that has a combined retail value of $679
- Two 1,000-foot spools of full mil-spec U.S.-made 750 paracord (in-stock colors only) from www.TOUGHGRID.com (a $240 value).
- Two Super Survival Pack seed collections, a $150 value, courtesy of Seed for Security, LLC.
- A transferable $150 FRN purchase credit from Elk Creek Company, toward the purchase of any pre-1899 antique gun. There is no paperwork required for delivery of pre-1899 guns into most states, making them the last bastion of firearms purchasing privacy!
Third Prize:
- A Berkey Light water filter, courtesy of USA Berkey Filters (a $305 value),
- A $300 gift certificate from Good2Goco.com, good for any of their products: Home freeze dryers, pressure canners, Country Living grain mills, Emergency Essentials foods, and much more.
- Three sets each of made-in-USA regular and wide-mouth reusable canning lids. (This is a total of 300 lids and 600 gaskets.) This prize is courtesy of Harvest Guard (a $270 value)
- A transferable $150 FRN purchase credit from Elk Creek Company, toward the purchase of any pre-1899 antique gun.
—
More than $875,000 worth of prizes have been awarded since we started running this contest. In 2023, we polled blog readers, asking for suggested article topics. Refer to that poll if you haven’t yet chosen an article topic. Round 112 ends on May 31st, so get busy writing and e-mail us your entry. Remember that there is a 1,500-word minimum, and that articles on practical “how-to” skills for survival have an advantage in the judging.